A Bitcoin mixer is a service that Bitcoin holders can use to make their BTC transaction history more difficult to trace. There are many Bitcoin mixing services available on the market, but not all of them are worth your time.
To help you narrow down your search, we have selected the 5 best Bitcoin mixers available right now.
Before we take a closer look at the list of the best Bitcoin mixers, let’s first learn about why Bitcoin is not actually very private and why Bitcoin mixers even exist.
List of the best BTC mixers in 2026:
- Mixero.io – A Bitcoin mixing service featuring an advanced privacy mode
- Wasabi Wallet – A Bitcoin wallet designed with privacy enabled by default
- Mixer.money – A Bitcoin mixer offering two distinct mixing options
- Tornado Cash – A decentralized cryptocurrency mixer built for Ethereum
- Railgun – A blockchain privacy solution powered by smart contracts
Bitcoin isn’t truly private
Some people who are new to cryptocurrency believe that Bitcoin is fully anonymous. That assumption isn’t entirely accurate.
At a basic level, Bitcoin appears anonymous because users don’t need to submit personal details to create a wallet or send transactions. The protocol itself doesn’t recognize real-world identities, as Bitcoin addresses are simply strings of characters with no inherent personal information attached.
However, Bitcoin operates on a fully transparent blockchain. This public ledger records every transaction ever made on the network. Anyone can use a blockchain explorer, such as Blockchain.com, to view transactions dating back to Bitcoin’s launch in 2009.
As a result, it’s incorrect to assume your Bitcoin activity is private just because your name isn’t directly tied to your wallet address on the blockchain.
For instance, if you purchased Bitcoin using fiat currencies like USD or EUR through a regulated exchange, you likely had to complete identity verification. When you withdraw your BTC to a personal wallet, the exchange maintains a record connecting your identity to that withdrawal address — even if the information isn’t publicly visible.
This data could potentially be exposed through insider leaks, cyberattacks, or legal requests from authorities. In short, while the blockchain itself doesn’t require identity information, real-world interactions often create traceable links.
What Bitcoin mixers do
Bitcoin mixers aim to improve privacy by making it difficult to trace where coins originated. In simple terms, mixers combine BTC from multiple users, shuffle them together, and redistribute equivalent amounts back to participants. They often randomize transaction sizes and introduce delays to complicate tracking.
The general concept is straightforward: you send BTC to a mixer and later receive roughly the same amount back (minus service fees), but the returned coins are much harder to associate with your original transaction.
The best Bitcoin mixers in 2026
Before using any mixing service, review the laws in your country. Crypto regulations vary significantly, and services that are permitted in one jurisdiction may be restricted in another.
Here’s our overview of the leading Bitcoin mixers available in 2026.
1. Mixero.io – Advanced privacy with optional Monero integration

Mixero.io is a CoinJoin-based Bitcoin mixing platform. It also offers an “advanced” mode that routes BTC through Monero (XMR) before converting it back to Bitcoin, providing an extra layer of obfuscation. This enhanced option comes with higher fees.
Users can increase their fee to prioritize their transaction and speed up processing. The standard CoinJoin fee starts at 0.7% plus a fixed 0.0003 BTC charge. The advanced XMR bridge option begins at 1.6% and can go up to 4.7% for faster execution. Users can also delay transactions for up to 168 hours (7 days).
In addition to BTC, Mixero supports ETH mixing, which may appeal to users seeking privacy tools for multiple major cryptocurrencies.
Key features:
- CoinJoin-based mixing with optional Monero bridge
- Advanced XMR mode for stronger privacy at higher cost
- Adjustable fees for faster processing
- Fees starting at 0.7% (standard) and 1.6% (advanced)
- Optional transaction delays up to 7 days
- Supports both BTC and ETH
2. Wasabi Wallet – Privacy-focused Bitcoin wallet

Wasabi Wallet is a non-custodial Bitcoin wallet that includes built-in CoinJoin functionality. As a non-custodial solution, users retain full control of their private keys.
CoinJoin transactions through Wasabi incur a 0.3% coordinator fee, in addition to standard Bitcoin network fees. However, the coordinator fee is waived for CoinJoin transactions under 0.01 BTC.
By default, Wasabi routes all network traffic through the Tor network to enhance privacy, though users can disable this option.
Key features:
- Built-in CoinJoin integration
- Non-custodial wallet with user-controlled keys
- 0.3% coordinator fee (waived for small transactions)
- Tor-enabled by default for network privacy
3. Mixer.money – Two privacy-focused mixing options

Operating since 2016, Mixer.money is a long-standing Bitcoin mixing service offering a simple interface and two primary modes: standard mixing and “complete anonymity.”
The standard option charges a randomized fee between 1% and 1.5% (to enhance privacy) and typically completes within two hours. It supports transactions between 0.001 and 1 BTC and uses funds from its user base for mixing.
The “complete anonymity” mode provides stronger privacy protections but costs between 4% and 5% and may take up to 10 hours. This mode sources liquidity from cryptocurrency exchanges.
Mixer.money is accessible via both the regular web and the Tor network. It also provides a Telegram bot that allows users to initiate mixing directly within Telegram.
Keep in mind that Mixer.money is centralized and therefore requires trust in the operator.
Key features:
- Active since 2016
- Two mixing modes (standard and enhanced privacy)
- Available through Tor
- Telegram bot support
4. Tornado Cash – Decentralized Ethereum-based mixer

Tornado Cash is a decentralized mixing protocol primarily built on Ethereum. It breaks the on-chain connection between sender and receiver by using smart contract pools.
Users deposit fixed amounts (such as 1 ETH or 100 ETH) into shared pools and later withdraw funds to a different address. Because many users deposit identical amounts, linking deposits and withdrawals becomes extremely difficult.
Tornado Cash supports multiple tokens and networks, although most activity occurs on Ethereum. By standardizing deposit amounts and pooling liquidity, the protocol strengthens anonymity as participation increases.
As of December 2025, Tornado Cash holds over $1 billion in total value locked, with ETH accounting for most of the funds, alongside assets like TORN, BNB, and DAI.
Key features:
- Smart contract-based privacy protocol
- Fixed-denomination deposit pools
- Multi-token and multi-network support
- Over $1 billion in total value locked
5. Railgun – Smart contract-powered privacy system
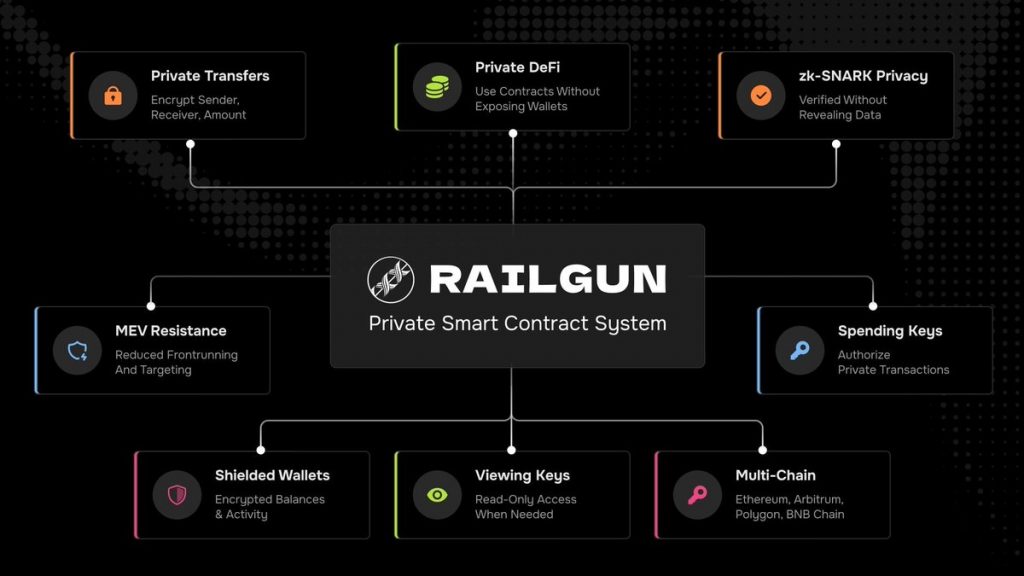
Railgun is a privacy-focused smart contract system that shields transaction data directly on-chain. It conceals key details such as sender, recipient, token type, and amount using Private Balances, which form a shared anonymity pool.
Transactions within the Railgun ecosystem appear to originate from this collective pool, making it challenging to determine who initiated a transfer or which assets were used.
Privacy improves as more users participate, increasing the anonymity set. Popular tokens like USDC or DAI generally provide stronger privacy due to higher usage compared to less common assets.
Railgun can be accessed through compatible wallets such as Railway Wallet, which supports zk-SNARK-powered private transactions without exposing balances.
Key features:
- Shields sender, recipient, token, and amount
- Uses Private Balances to expand anonymity set
- Privacy increases with user participation and TVL
- Accessible via zk-SNARK-enabled wallets
Are Bitcoin mixers legal?
In many countries, Bitcoin mixers are not explicitly illegal. However, most do not implement Know Your Customer (KYC) or anti-money laundering (AML) procedures, placing them in a regulatory gray area.
Unless a service is specifically prohibited, users typically won’t face legal consequences simply for using a mixer. That said, authorities have shut down numerous mixers over the years, and several operators have been arrested.
While mixers can serve legitimate privacy needs, they are also used by criminals — for example, hackers attempting to launder stolen funds. This association has made them highly controversial.
Notable enforcement actions include:
- Bestmixer.io shut down by Europol and Dutch authorities (2019)
- Bitcoin Fog operator arrested and charged in the U.S. (2021)
- Tornado Cash sanctioned by OFAC (2022), with sanctions lifted in 2025
- ChipMixer taken down by U.S. and German authorities (2023)
Are Bitcoin mixers safe?
Safety largely depends on the specific service used. Centralized mixers require trust that operators will not misappropriate user funds.
It’s also important to recognize that mixing does not guarantee perfect anonymity. The effectiveness of privacy measures varies by implementation, and blockchain analysis tools continue to evolve. In some cases, investigators may still trace coins that have passed through mixers.
Additionally, some cryptocurrency platforms and businesses may flag or restrict wallets associated with mixing services.
Conclusion: Mixers address Bitcoin’s privacy limitations
Bitcoin is pseudonymous rather than fully anonymous, and transactions can be traced under close examination. Mixing services aim to make blockchain activity more difficult to analyze, giving users greater financial privacy.
However, because mixers are sometimes used for illicit purposes, they remain controversial and frequently attract regulatory scrutiny — even in jurisdictions where they are not outright banned.